Take Control of Your Company's Passwords and Accounts.
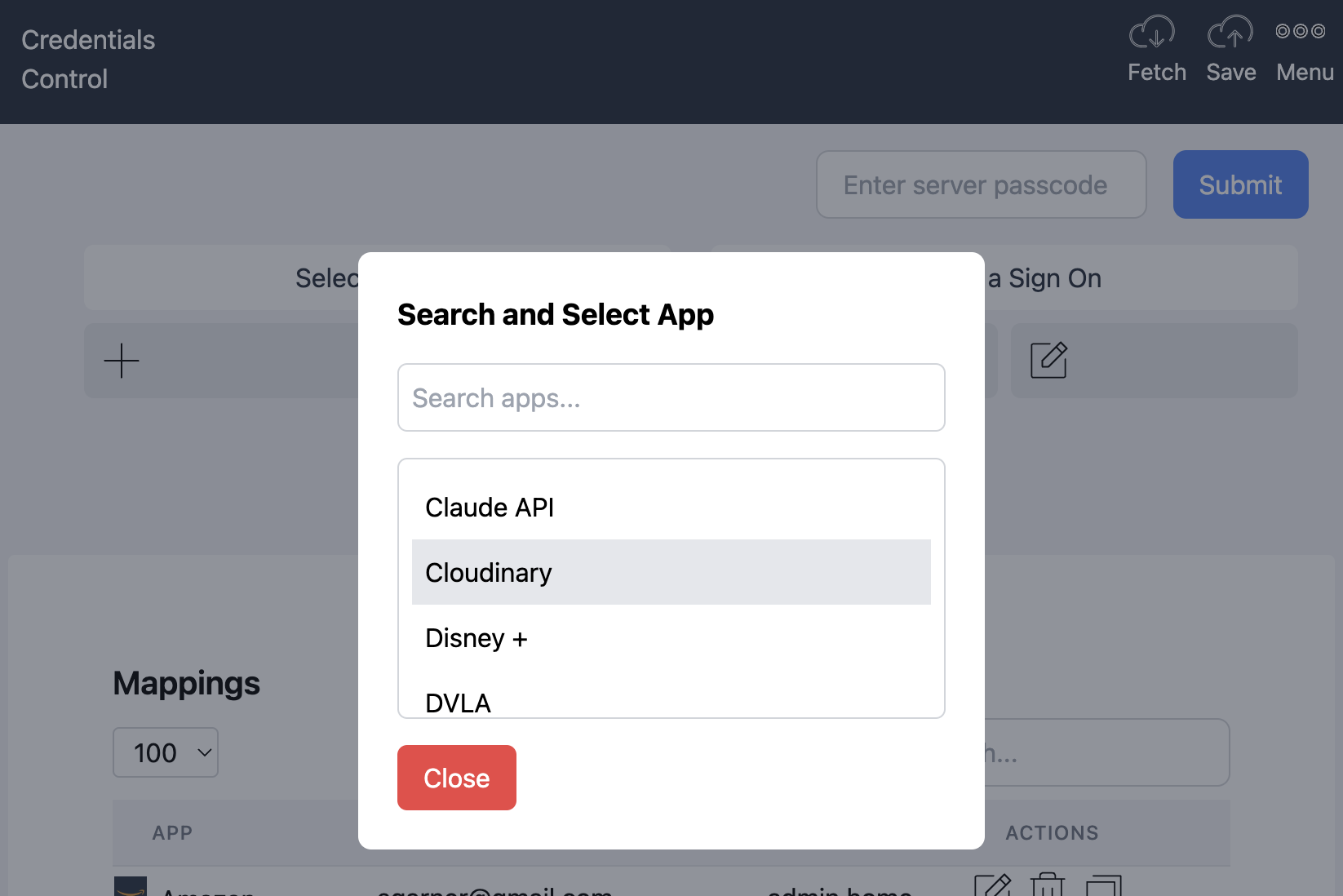
No SSO, No Enterprise Complexity, Just Visibility.
WHDIGO gives SMEs a single place to track SaaS subscriptions, shared credentials, and account ownership — ensuring continuity when employees leave or subscriptions change.